By the end of this course you will be fully aware of the wired and wireless computer networks basics, devices, and protocols in a step-by-step pace. You will also reach the professional level in networks security in terms of concepts, technologies, and tools. The course requires no background or pre-requisite, yet you will be able to understand all the up-to-date terminologies in the networks security during the lectures.
This course is organized as follows:
Section One: Introduction to Computer Networks
•Lecture 1: What is a Computer Network?
•Lecture 2: Computer Networks Topologies
•Lecture 3: Computer Networks Categories
•Lecture 4: Computer Networks Devices and Services
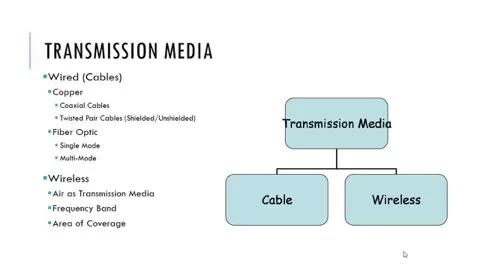
•Lecture 5: Computer Networks Transmission Media
Section Two: ISO/OSI Model (7 Layers)
•Lecture 1: Why ISO/OSI Model?
•Lecture 2: Application, Presentation, and Session Layers
•Lecture 3: Transport and Network Layers
•Lecture 4: Data Link and Physical Layers
•Lecture 5: ISO/OSI Model in Action
Section Three: TCP/IP Protocol Suite
•Lecture 1: Introduction to Computer Networks Protocols
•Lecture 2: IP Protocol
•Lecture 3: TCP and UDP Protocols
•Lecture 4: Application Protocols
•Lecture 5: TCP/IP Characteristics and Tools
Section Four: Wireless Networks
•Lecture 1: Wireless Networks Benefits
•Lecture 2: Wireless Networks Types
•Lecture 3: Wireless Networks Protocol (Wi-Fi)
•Lecture 4: Wireless Networks Devices
•Lecture 5: Wireless Networks Drawbacks
Section Five: Computer Networks Security
•Lecture 1: Security Goals
•Lecture 2: Securing the Network Design
•Lecture 3: TCP/IP Security and Tools
•Lecture 4: Port Scanning and Tools
•Lecture 5: Sniffing and Tools
Section Six: Firewalls and Honeypots
•Lecture 1: Why Using a Firewall?
•Lecture 2: Firewalls Rules
•Lecture 3: Firewalls Filtering
•Lecture 4: Honey Pots
•Lecture 5: Bypassing Firewalls
Section Seven: Intrusion Detection and Prevention systems (IDS/IPS)
•Lecture 1: What is Intrusion Detection Systems (IDS)?
•Lecture 2: Network IDS (NIDS)
•Lecture 3: NIDS Challenges
•Lecture 4: Snort as NIDS
•Lecture 5: Intrusion Prevention Systems (IPS)
Section Eight: Wireless Networks Security
•Lecture 1: Wired Equivalent Privacy WEP Attacking
•Lecture 2: WPA and AES Protocols
•Lecture 3: Wireless Security Misconceptions
•Lecture 4: Wireless Attacks and Mitigation
•Lecture 5: Secure Network Design with Wireless
Section Nine: Physical Security & Incident Handling
•Lecture 1: Physical Security Objectives
•Lecture 2: Physical Threats and Mitigation
•Lecture 3: Defense in Depth (DiD)
•Lecture 4: What is an Incident?
•Lecture 5: Incident Handling
Section Ten: Computer Networks Security Conclusion
•Lecture 1: Confidentiality, Integrity, and Availability (CIA)
•Lecture 2: Assets, Threats, and Vulnerabilities
•Lecture 3: Risks and Network Intrusion
•Lecture 4: Common Attacks
•Lecture 5: Security Recommendations